Email Threat Detection & Response
Automatically stop attacks that bypass your secure email gateway.
Powered by Intelligence from the only global network of 35+ million users.
Defend against advanced threats with Cofense Phishing Detection & Response.
Gain critical insights to prioritize your investigations, conduct your own threat hunting, and automatically remove threats before they reach users' inboxes.
Automatically Detect and Stop Attacks
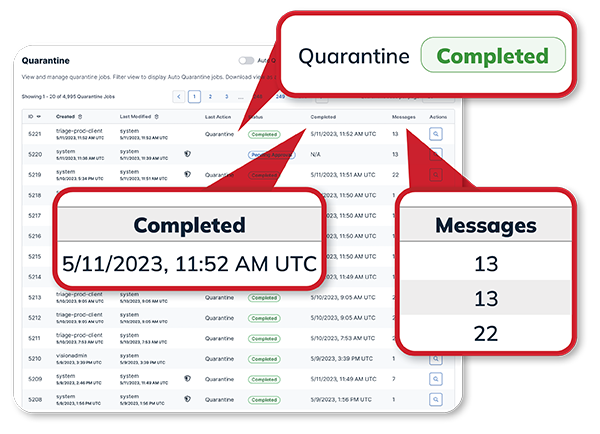
Quarantine email threats across your organization in minutes.
- Quarantine every instance of malicious emails and stop the attack in its tracks, including emails not reported by your users thanks to a global network of more than 35+ million reporters.
- Supports complex queries to find the most dangerous polymorphic attacks evading SEGs.
- Increase speed of investigations by conducting your own threat hunting with unique IOC Wild Card Matching that helps you uncover today’s most advanced email threats and take action to remediate them.
Supercharge Your SOC
Prioritize & remediate real email threats fast.
- Arms your SOC with actionable intelligence and contextual information to help prioritize SOC workloads, and reduce noise so SOC analysts can focus on the most critical threats facing your organization.
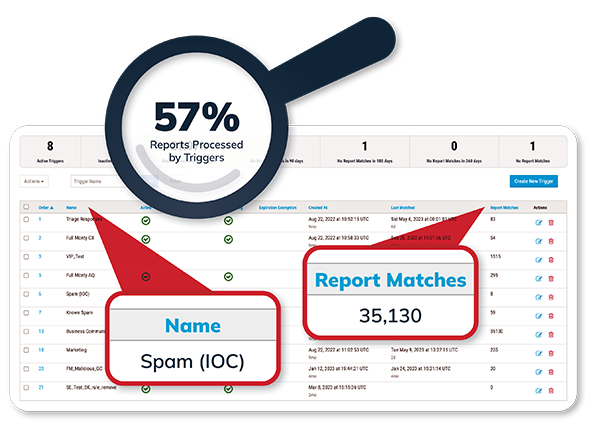
- Reduce dwell time: as soon as a suspicious email gets reported, thousands of intelligence-driven YARA rules automatically assess the report, clustering it with reports containing similar payloads, and surfacing the highest priority threats for immediate action.
- Triggers have been added for easy build, allowing any SOC team member to immediately begin automating.
Actionable Threat Intelligence
Leverage timely and accurate email threat insights to avoid a breach.
- Augment and enhance the capabilities of your security technology stack by integrating Cofense Intelligence feeds into your SIEMs, TIPs and SOARs.
- Reduce dwell time with contextualized insights and a threat intelligence accuracy of 99.9996%.
- Arm your team with advanced threat hunting capabilities through ThreatHQ, Active Threat Reports and access to our comprehensive IOC database.
- Decrease Mean-Time-To-Detection (MTTD) and Mean-Time-To-Respond (MTTR) with human-vetted intelligence allowing your SOC to focus on remediation and automation for known threats.

Managed Phishing Detection & Response
Are you faced with limited resources to effectively defend against and remediate phishing attacks?
We provide threat analysis, investigation, and response services for you, acting as an extension of your security operations team.