Today, PhishMe’s analysts identified a new banking Trojan that is based heavily on the GameOver Zeus binary. The GameOver Zeus mutation was distributed as an attachment in three spam email templates, utilizing the simplest method of infection to compromise end users’ systems.
The E-mail spam campaign
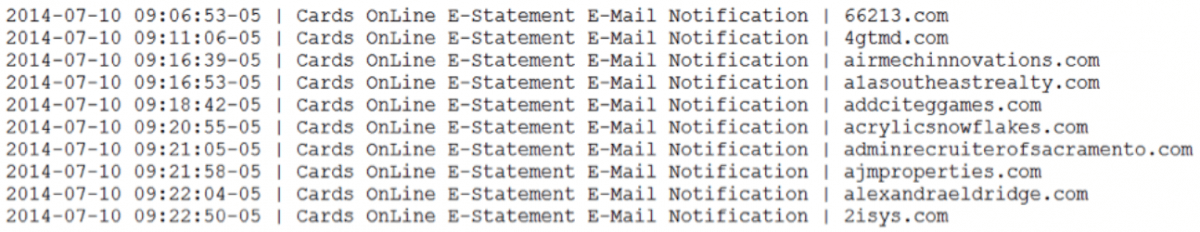
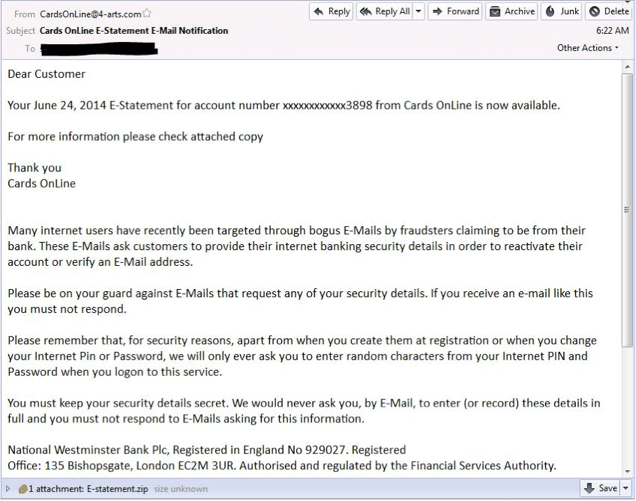
From 9:06 AM to 9:55 AM we intercepted spam messages claiming to have been sent from NatWest Bank.
One of the email messages used to distribute the new GameOver Zeus variant is listed below. As you can see, the message uses a common social engineering technique. It alerts the recipient to the risk of bogus emails and advises the recipient to be on their guard. It even provides information to help the bank’s customers avoid becoming a victim of cybercrime. Of course, the email does not mention not opening email attachments from unknown or suspicious sources, such as 4-arts.com.
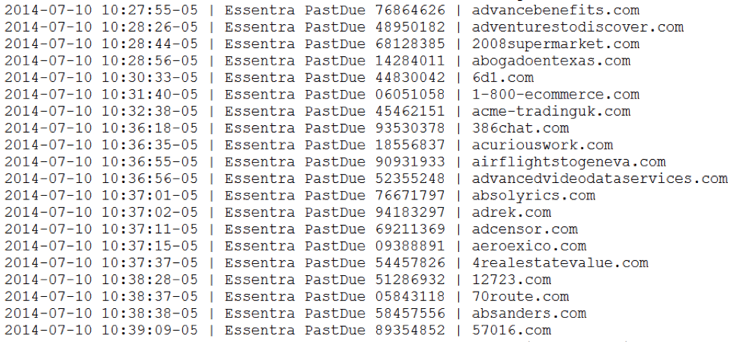
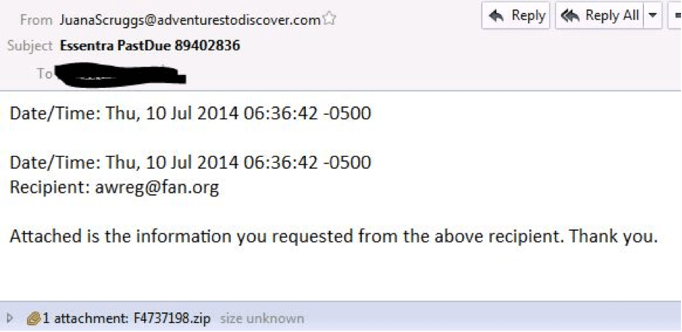
From 9:34 AM to 10:50 AM we saw spam messages with the subject “Essentra PastDue” like these:
This message was far more succinct and to the point. Claiming that the attached file had actually been requested by the recipient of the message.
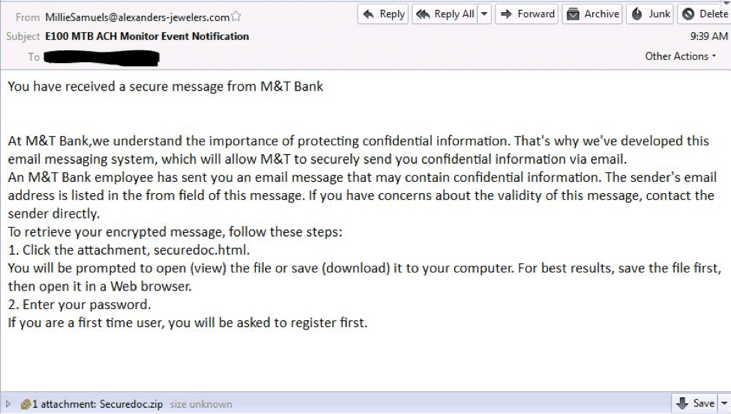
The longest lasting of the spam campaigns was imitating M&T Bank, with a subject of “E100 MTB ACH Monitor Event Notification. That campaign is still ongoing at the time of writing.
The final message was also sent from a suspicious domain. The email is poorly formatted, there is no branding, and there is no signature on the email – all common signs that the email is not genuine. However, a curious M&T bank customer who lacks security awareness may open the email attachment following the instructions provided. Opening the file in a web browser will result in infection with the Trojan.
The malicious payload
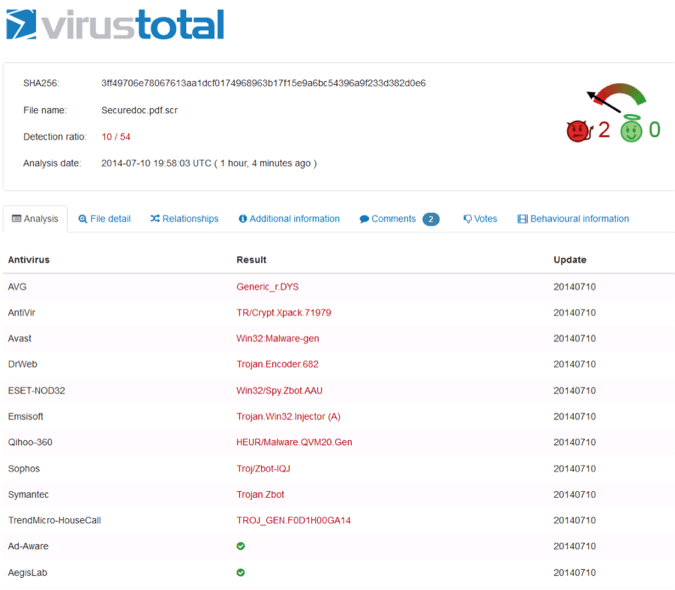
The three spam campaigns each had a .zip attachment. Each of those compressed files contained the same file, which was a form of “.scr” file with the hash:
MD5: 5e5e46145409fb4a5c8a004217eef836
At this timestamp (1600 Central time, 7 hours after we first noticed the spam campaign) the detection rate at VirusTotal was 10/54 – Still very low. Relatively few anti-virus vendors had identified the file as malicious.
When the attachment is opened the malware payload is executed. The malware attempts to make contact with certain websites in accordance with a domain generation algorithm. The goal of these contact attempts is to connect to a server that provide instructions to the malware. Many sandboxes would have failed to launch the malware, as the presence of VMWare Tools will stop the malware from executing. Other sandboxes would not have noticed the successful connection, because the malware took between 6 and 10 minutes to randomly generate the single domain name that was used to launch the new Zeus Trojan and download its bank information “webinject” files from the attackers C&C server.
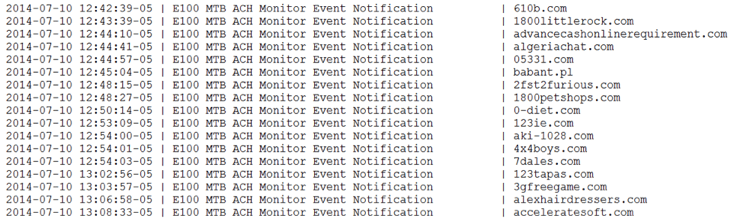
The Domain Generation Algorithm is a method used by cybercriminals to regain access to their chosen botnet. Based on the current date, random-looking domain names are calculated and the malware reaches out via the Internet to see if that domain exists. Examples of these are listed below:
bmo0ve7lxujkiid9sycsfxb.biz
borwxz16ctey4fmc99y1t8nw9s.biz
bttkygongoew1himlrd1889yui.net
bzi7vw1f0iw5r1qy1pax1sgl3z0.biz
c1xjo91vug07xhbrht291yzkb.com
c1yc37z0h5rf18h0aw7nib2f.org
c4j59h1voxihj4rntttdl7cn.org
c6p7902ciu9y5hiqgcn2xlqz.net
c77nf4hwksy8iy325isrrjo.net
cc5y751uyzepi1wud8mk1iwksux.com
cfdw9oj4vhr1ktr2je1pf2rq8.org
cfs50p1je5ljdfs3p7n17odtuw.biz
ci0zfurp5trgvec4mn1tvlong.net
cjjnhq19ux8jm71iekc1lnkqai.biz
cjn50rx5y60b1o4d3xiibdkhl.net
ckjxnwhjbp8tcg1rb351wqed.net
cnhi1zulqoekn08s8oibii8i.org
coaa131phdgaq1wpj3a31gdcqjp.net
cx8y001jigv7y1pjnlcw452pv0.net
cxotoovt355vgearpv1xi2jdy.biz
cy0bj11yfrfma137tqlqh2fryo.net
cz7fn21k15vgkmem3j2p0ip7q.org
czz0wl1uxb3dk1niyev410qqhk.biz
d6y5enamrkg4zavi2t146s40h.biz
PhishMe’s analysts have confirmed with the FBI and Dell SecureWorks that the original GameOver Zeus is still “locked down”. This new DGA list is not related to the original GameOver Zeus, although it bears a striking resemblance to the DGA utilized by that Trojan, suggesting this is a new GameOver Zeus variant. In addition to a new DGA, the malware seems to have traded its Peer to Peer Infrastructure for a new Fast Flux-hosted C&C strategy.
The successful domain: cfs50p1je5ljdfs3p7n17odtuw.biz was registered this morning in China with the registrar “TodayNIC.com”:
Domain Name: CFS50P1JE5LJDFS3P7N17ODTUW.BIZ
Domain ID: D61087891-BIZ
Sponsoring Registrar: TODAYNIC.COM, INC.
Sponsoring Registrar IANA ID: 697
Registrar URL (registration services): www.todaynic.biz
Domain Status: clientTransferProhibited
Variant: CFS50P1JE5LJDFS3P7N17ODTUW.BIZ
Registrant ID: TOD-43737096
Registrant Name: Whois Agent
Registrant Organization: Whois Privacy Protection Service
Registrant Address1: Xiamen
Registrant City: Xiamen
Registrant State/Province: FUJIAN
Registrant Postal Code: 361000
Registrant Country: China
Registrant Country Code: CN
Registrant Phone Number: +57.59222577844
Registrant Facsimile Number: +57.59222577844
Registrant Email: [email protected]
Name Server: NS1.ZAEHROMFUY.IN
Name Server: NS2.ZAEHROMFUY.IN
Created by Registrar: TODAYNIC.COM, INC.
Last Updated by Registrar: TODAYNIC.COM, INC.
Domain Registration Date: Thu Jul 10 09:26:06 GMT 2014
Domain Expiration Date: Thu Jul 09 23:59:59 GMT 2015
Domain Last Updated Date: Thu Jul 10 09:26:07 GMT 2014
In the original GameOver Zeus, the domain generation algorithm and its associated command and control resources, serve the botnet as a fallback to the peer-to-peer botnet which is this malware’s primary means of distributing instructions to infected machines. Using the websites associated with the domain generation algorithm, the GameOver botnet operators are able to distribute commands to infected machines that have lost contact with the peer-to-peer botnet.
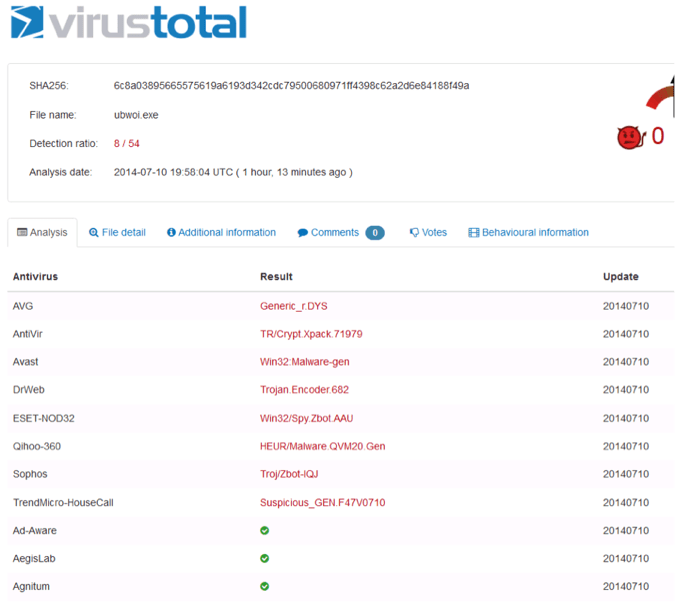
The binary that is dropped and injected into Internet Explorer after contacting the C&C receives a random name. The version seen this afternoon is currently detected by 8 of 54 AV products at VirusTotal, although others may detect it using non-signature based methods.
A little over a month ago, the GameOver Zeus botnet suffered a major blow as law enforcement carried out a takeover of the domains associated with the domain generation algorithm and made efforts to remove this malware from infected machines. Both actions severely limited the ability of the botnet operators to issue commands to victims’ machines.
Those efforts seemed to halt the spread of this dangerous malware and led to its disappearance from malicious spam emails, albeit only temporarily.
PhishMe was able to identify a number of the command-and-control hosts believed to be involved in the attacker’s attempt to revive the GameOver botnet. Following contact with any of these hosts, the malware began to exhibit behaviors characteristic of the GameOver Trojan—including using the characteristic list of URLs and URL substrings used for Web injects, form-grabs, and its other information stealing capabilities.
This discovery indicates the criminals responsible for GameOver’s distribution do not intend to give up on their botnet, even after suffering one of the most expansive botnet takeovers/takedowns in history.
As always, PhishMe researchers are closely monitoring the situation and will provide meaningful threat intelligence when there are further developments with the GameOver Zeus Trojan and its new variants.