One of the most historically effective techniques for gaining new infections for the powerful Dridex botnet malware has been sizable sets of widely-distributed phishing email. While these large campaigns have been intermittent for several months, the past week’s Dridex distributions have shown a renewed vigor with several larger campaigns being launched both concurrently and repeatedly. Many of these campaigns return to well-used and previously-successful email templates and malware delivery tools that had seen earlier utilization in conjunction with both Dridex deliveries and the delivery of other malware tools.
On March 30, 2017 three distinct sets of phishing emails were identified as delivering the Dridex malware. Each was a rehashing of a previously-used phishing narrative. The emails analyzed for Threat ID 8692 pretended to represent communication from a travel agency based in the United Kingdom confirming the recipient’s vacation travel has been booked. Other emails, delivered concurrently, purposed to deliver a vaguely- described “confirmation” as analyzed in Threat ID 8693. Furthermore, Threat ID 8700 documents a set of messages purporting to deliver a notice that an image attachment was ready for sending in yet another vague phishing narrative. Examples of these messages can be seen in Figure 1.
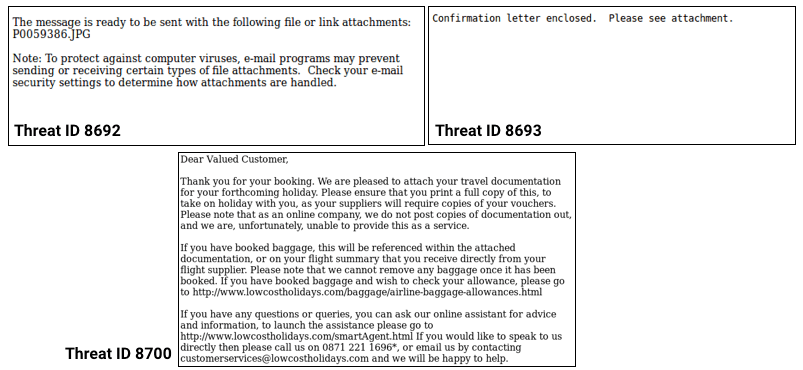
The message narrative used in these campaigns should be familiar to information security professionals following Dridex as they represent similar themes to earlier Dridex campaigns. The impersonation of small- and medium-sized firms based in the United Kingdom was previously a common theme among Dridex delivery emails. This preference in content may serve to indicate a preference for a population with which those emails are meant to have disproportionate appeal. However, it appears that these emails were still delivered globally. The other repeated narrative seen once again today is a vague informational message about the status of an image attachment that has been readied for sending. Similar narratives have been used a half-dozen times in the delivery of Dridex since July 2015.
While the Dridex botnet malware’s users are launching phishing campaigns with renewed vigor, their stories and tools have stayed the same. This provides a distinct advantage to threat intelligence users who have access to repositories of information on the tactics, techniques, and procedures related to earlier attacks. It also provides an advantage to organizations whose email users are prepared and empowered to identify and report suspicious emails. Empowered recipients of messages like these are able to recognize the lure and instead of becoming victims, can make a difference for their organization by reporting the email.
Emails based on the threats shown in this blog post are also available as templates in PhishMe Simulator.
For further information on the Threat ID’s mentioned in this post, PhishMe Intelligence customers can log into https://www.threathq.com.
For more information on PhishMe’s human vetted, phishing-specific threat intelligence request a demo today.


