(VIDEO UPDATE LINK: Defending Against Phishing Attacks: Case Studies and Human Defenses by Jim Hansen
• A human centric method of defense
• Attack case studies & attacker technique analysis
• Proactive simulation methods: educating workforces & detecting / thwarting attacks)
(^ say that title ten time fast)
Every year PhishMe Simulator sends millions of phishing emails to its 500+ enterprise customers’ employees worldwide. PhishMe is hands down the most robust and sophisticated phishing platform in existence. To say that we are a little obsessive about Phishing is a bit of an understatement. In fact, we are sitting on innovations in phishing that the bad guys have yet to figure out.
The difference in PhishMe emails versus the bad guys, is that ours are carefully crafted to deliver a memorable experience. Our experiences are masterfully designed to change human behavior to avoid phishing. So what happens when one of our own employees is on the receiving end of a wire fraud phish? Read on…
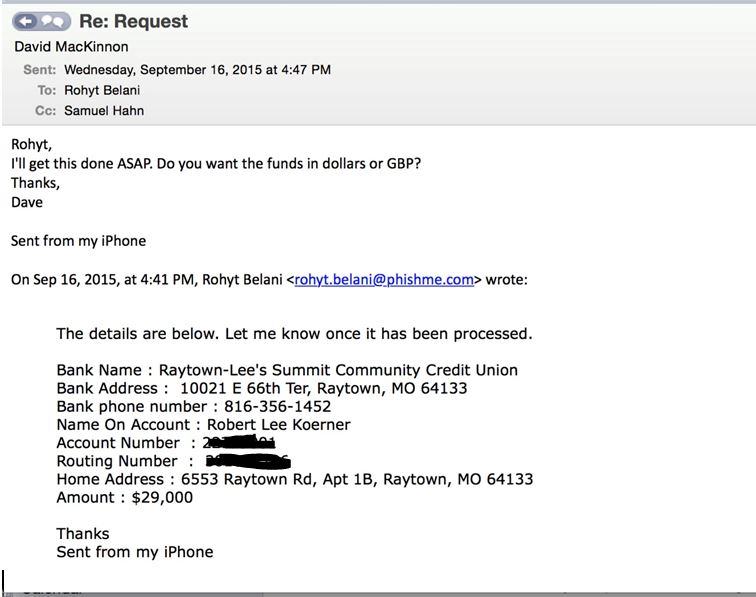
Yesterday our VP of Finance received an email that appeared to be from our CEO requesting a wire transfer:
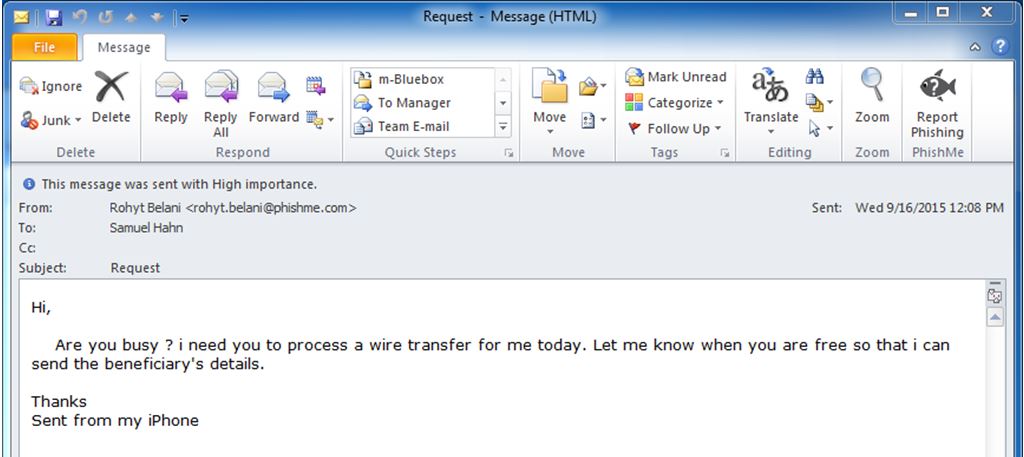
There were a number of oddities that stood out about this email, but there are a few interesting bits I want to call out. The attacker researched our company. He had the name of our CEO and our VP of Finance. He also correctly spoofed the CEO’s email address.
If the attacker is asking Sam to reply to a spoofed From: line, then the email will go back to Rohyt and not the attacker, right? Let’s examine the experience when we hit Reply:
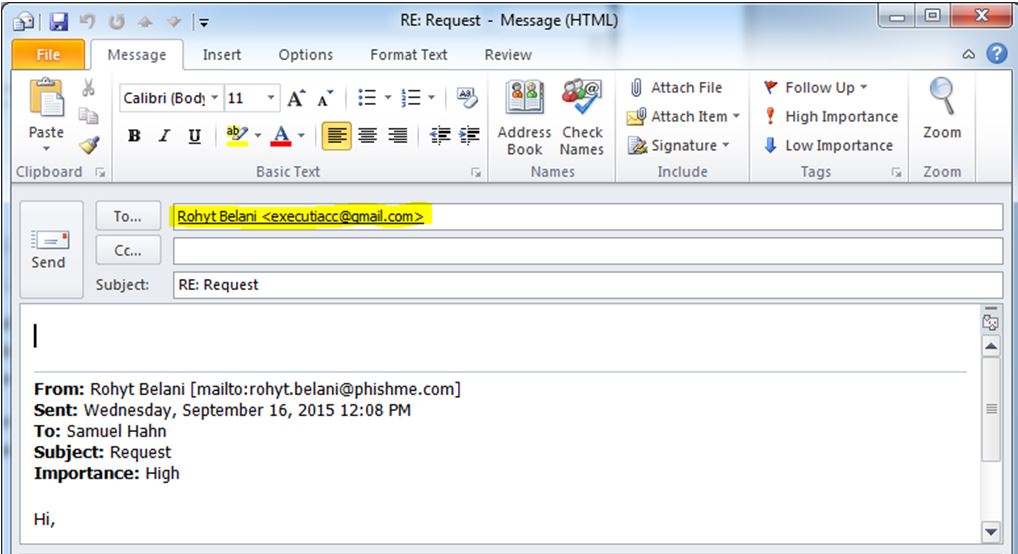
To: Rohyt Belani <[email protected]>
Where did that come from?
(Before I continue, let’s take a moment to breath in the irony of this. Clearly, the attacker researched our company. Yet, in his research it didn’t register that phishing the undisputed heavy weight champion of phishing was probably going to end badly? And that we regularly burn malware campaigns on our blog? Seriously! What did this guy think would happen? How many times was this attacker dropped on his head as a child?)
Sam didn’t hit reply. Instead, he used PhishMe Reporter in Outlook to immediately report the scam, where our analysis platform Triage picked it up. Here is what Sam’s report looked like in Triage:
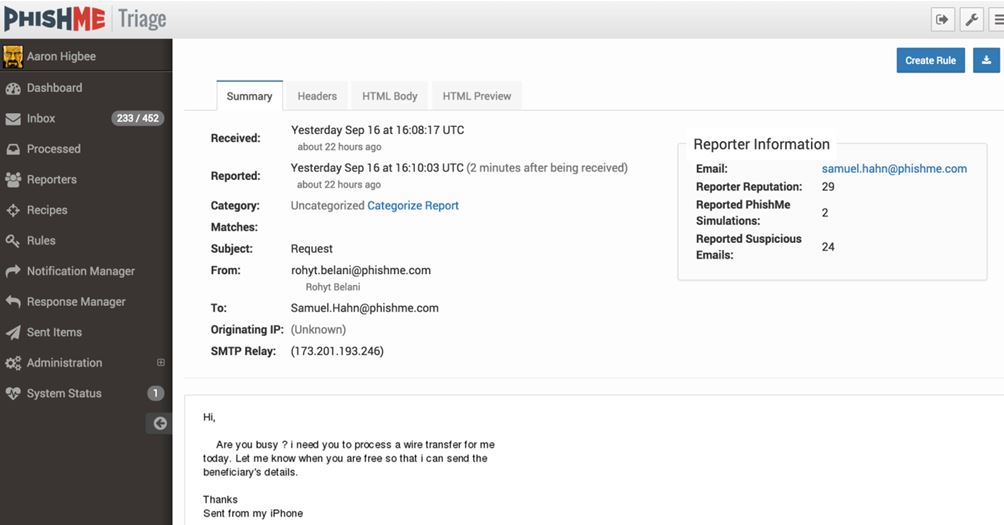
If we cruise on over to the Headers Tab in Triage, we can see how the attacker pulls off spoofing the From: line of rohyt.belani_at_phishme (dot) com, yet is still able to capture a reply by inserting a Reply-To: header:
Reply-To: Rohyt Belani <[email protected]>
The attacker wants a reply, and a reply he shall receive! We have two goals. One to capture the receiving banking details so we can notify law enforcement, and second, to determine if we are dealing with a human or an automated script. Sam sends an email back to attacker – “Rohyt” asking Dave to process the wire. (Dave’s title is on LinkedIn. Seriously attacker, do you think our Director of Incident Response sends wires?…)

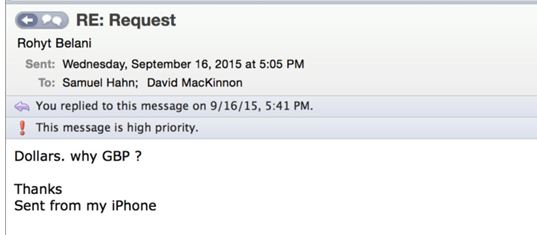
Goal 1 achieved. We get a response back that has the banking details, so we move on with our test to determine if we are dealing with a human or bot, by asking for clarification on currency type:
Cha-Ching! Confirmation we have a human on the other end of our scam:
At this point we could have left well enough alone. If only we had a platform to send a phishing email to the attacker that we could use to extract his IP address. Oh wait! We do! (again the irony…) So we fire up PhishMe Simulator and build a phish to send the attacker. First, we create a phishing link that looks official:
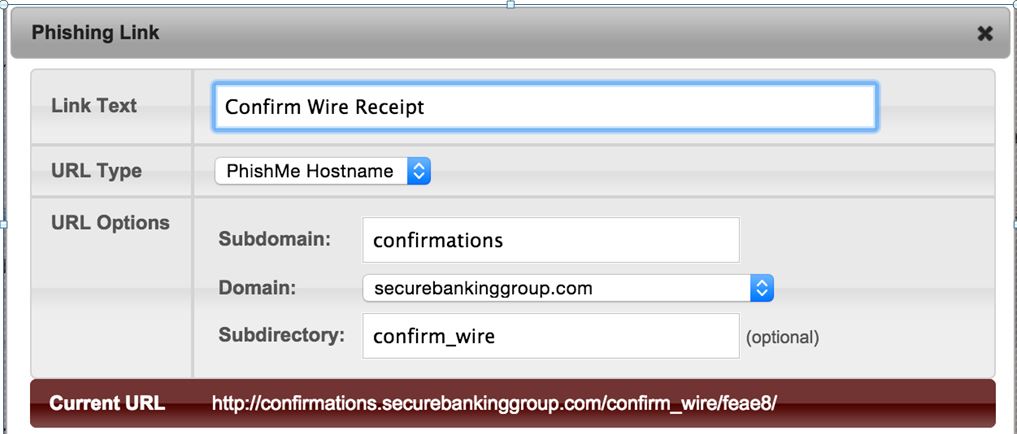
Then, we craft a phishing email and send it to the attacker “Rohyt” to confirm the wire.
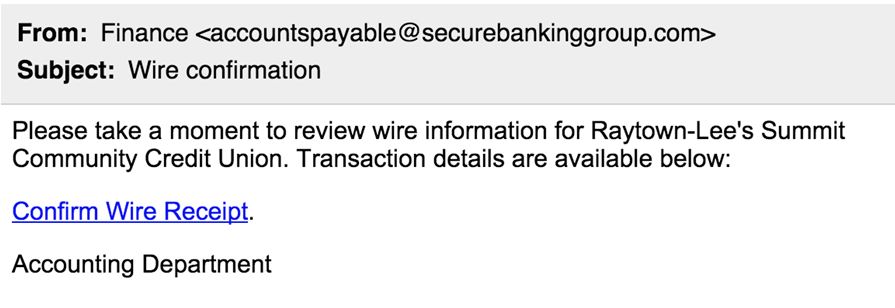
Forgive our total lack of surprise at this point, when the attacker clicks our Phishing link and we extract his Host and IP address information:
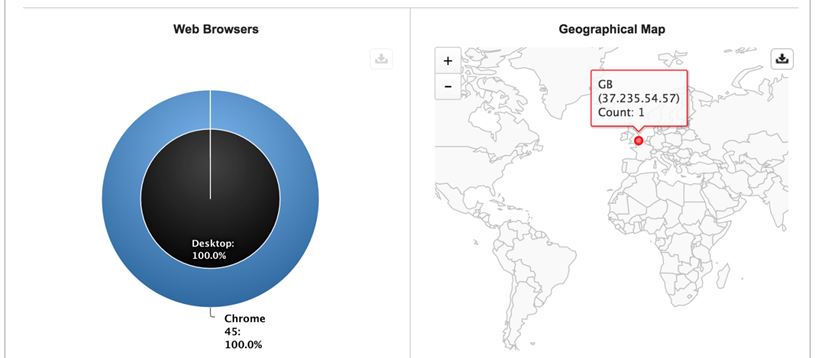
The attacker took our bait and clicked our phishing link exposing his exit IP address in the UK, which we immediately forwarded to law enforcement.
Summary
We may never know why this fraudster thought phishing the authority on all-things-phishing was going to be successful, but unfortunately for many others, these wire fraud phishing emails are wildly successful. On August 27, 2015 the FBI put out a Public Service Announcement about Business Email Compromise, which specifically warns about this very scam detailed in this blog post.
Previously covered by Brian Krebs, it’s estimated that over $1.2 billion has been lost due to similar phishing emails.
- Intrusion Prevention Systems did not stop this attack.
- Application White Listing did not stop this attack.
- Two-Factor Authentication did not stop this attack.
- Sandbox technology did not stop this attack.
- Next-Generation endpoint protection did not stop this attack.
- URL-Rewriting did not stop this attack.
- Big-Data-Machine-Learning-Hadoop-Clusters did not stop this attack.
Samuel Hahn – VP of Finance, conditioned to recognize phishing emails through PhishMe Simulator and armed with Reporter, stopped this attack.